So it seems like just yesterday that pfSense 2.2 came out after a long standing release of 2.1.5, and now 2.2.1 has arrived.
This release contains both security and bug fixes. Here are some highlights:
Security Fixes
- pfSense-SA-15_02.igmp: Integer overflow in IGMP protocol (FreeBSD-SA-15:04.igmp)
- pfSense-SA-15_03.webgui: Multiple XSS Vulnerabilities in the pfSense WebGUI
- pfSense-SA-15_04.webgui: Arbitrary file deletion vulnerability in the pfSense WebGUI
- FreeBSD-EN-15:01.vt: vt(4) crash with improper ioctl parameters
- FreeBSD-EN-15:02.openssl: Update to include reliability fixes from OpenSSL
Bug Fixes
- General
- Rules / NAT
- IPsec
- OpenVPN
- DNS Resolver
- Logging
- Traffic Shaping
- IPv6
- VIP/CARP
- Misc Binary/OS Changes
A note on the OpenSSL “FREAK” vulnerability:
- Does not affect the web server configuration on the firewall as it does not have export ciphers enabled.
- pfSense 2.2 already included OpenSSL 1.0.1k which addressed the client-side vulnerability.
- If packages include a web server or similar component, such as a proxy, an improper user configuration may be affected. Consult the package documentation or forum for details.
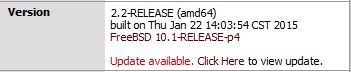
This blog runs behind a virtual pfSense 2.2 instance and upgrading was as simple as logging into the web UI and choosing the “click here” to update. Been running for 24 hours without an issue!
There’s no particular feature that appealed to me in 2.2.1 it’s just that I prefer to run the latest version considering I am running webservers and such. You can auto upgrade from 2.2 but be careful if you upgrade from 2.1.x there are some things that change in the configuration! Please read the pfSense documentation on upgrading before attempting!
 I am a Sr. Systems Engineer by profession and am interested in all aspects of technology. I am most interested in virtualization, storage, and enterprise hardware. I am also interested in leveraging public and private cloud technologies such as Amazon AWS, Microsoft Azure, and vRealize Automation/vCloud Director. When not working with technology I enjoy building high performance cars and dabbling with photography. Thanks for checking out my blog!
I am a Sr. Systems Engineer by profession and am interested in all aspects of technology. I am most interested in virtualization, storage, and enterprise hardware. I am also interested in leveraging public and private cloud technologies such as Amazon AWS, Microsoft Azure, and vRealize Automation/vCloud Director. When not working with technology I enjoy building high performance cars and dabbling with photography. Thanks for checking out my blog! 
